Multi-Stage Attack Disruption
MultiStage, Wide-Area Attack Disruption
ThreatStryker helps you detect multiple stages of an attack and provides protection policies to disrupt those attacks at various stages.
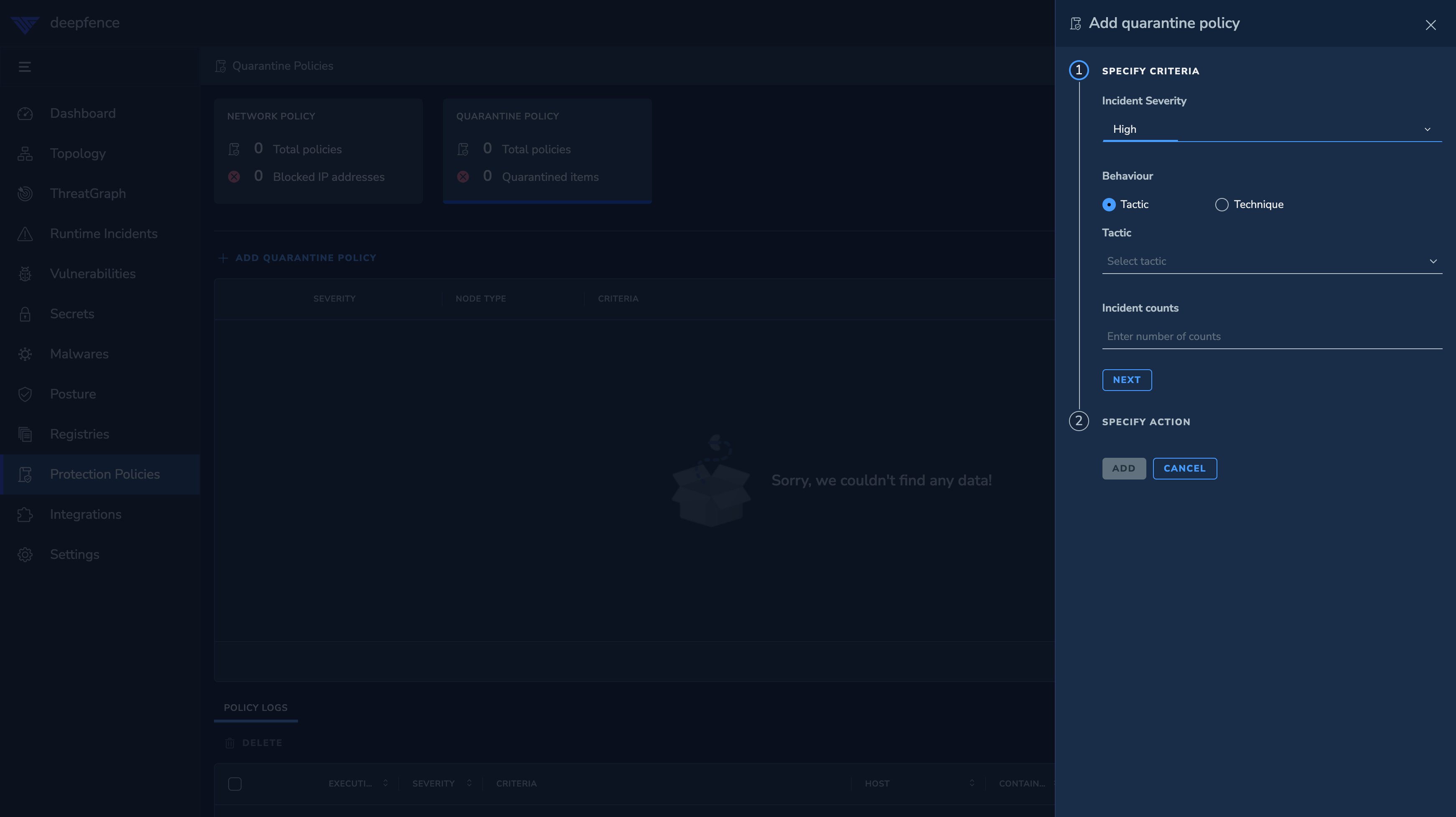
Quarantine Policies
Quarantine policies enable reset, pause and decommissioning of infected containers, pods or virtual machines:
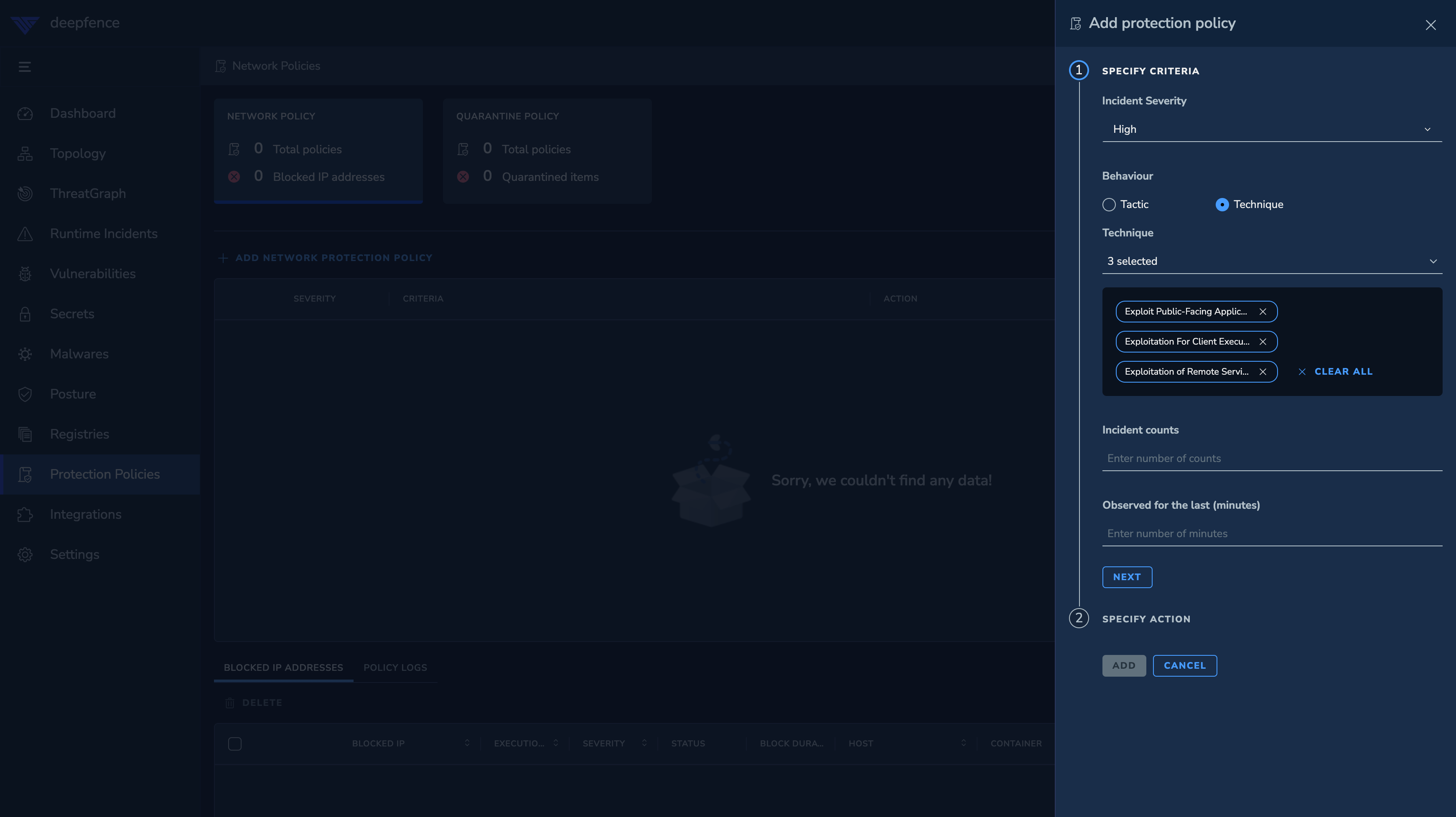
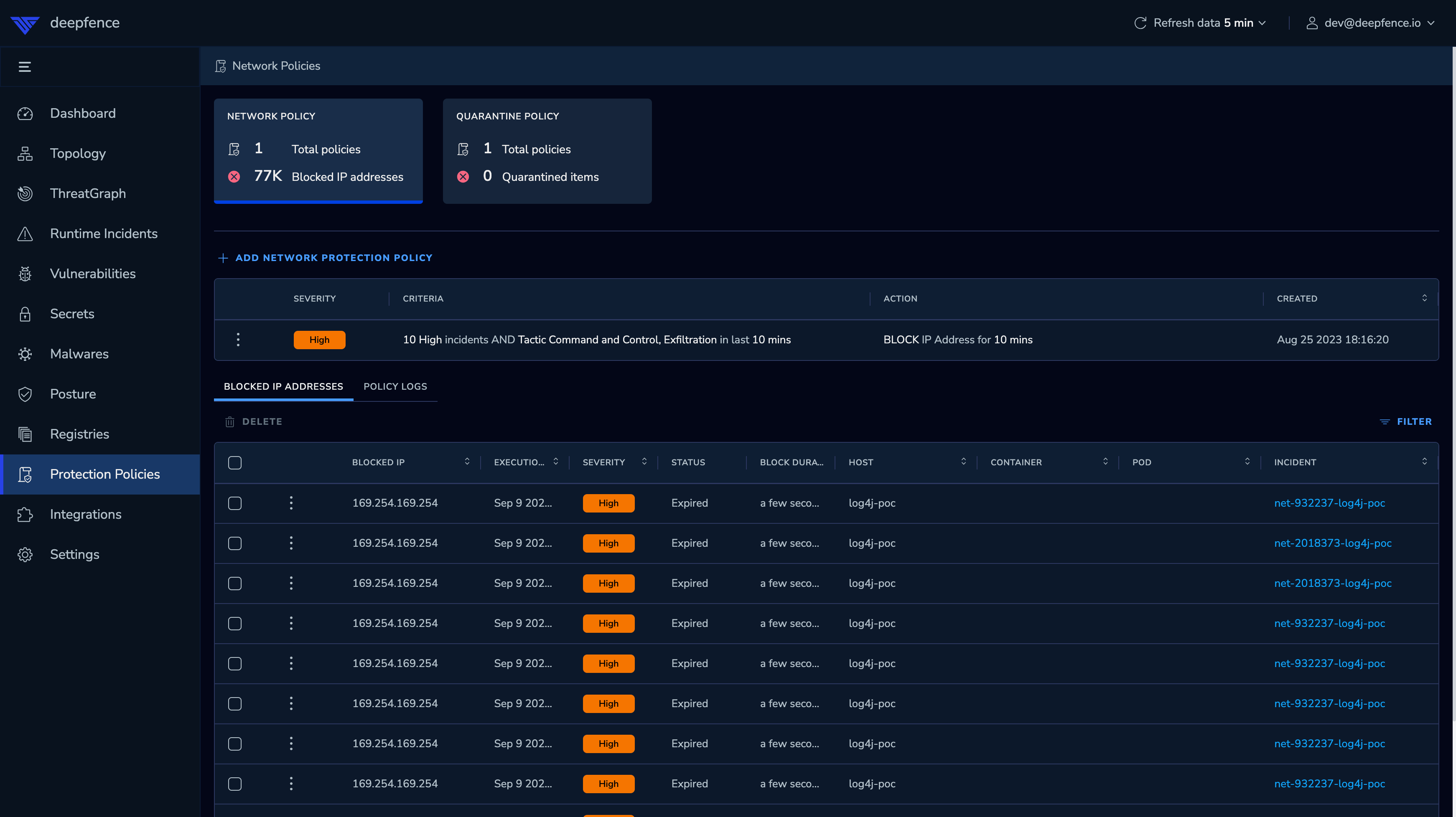
Network Policies
Network policies enable blocking external as well as internal attackers on their tracks. Protection Policy can be enforced using deepfence agent or Cloud WAF. By default, it is enforced by deepfence agent.
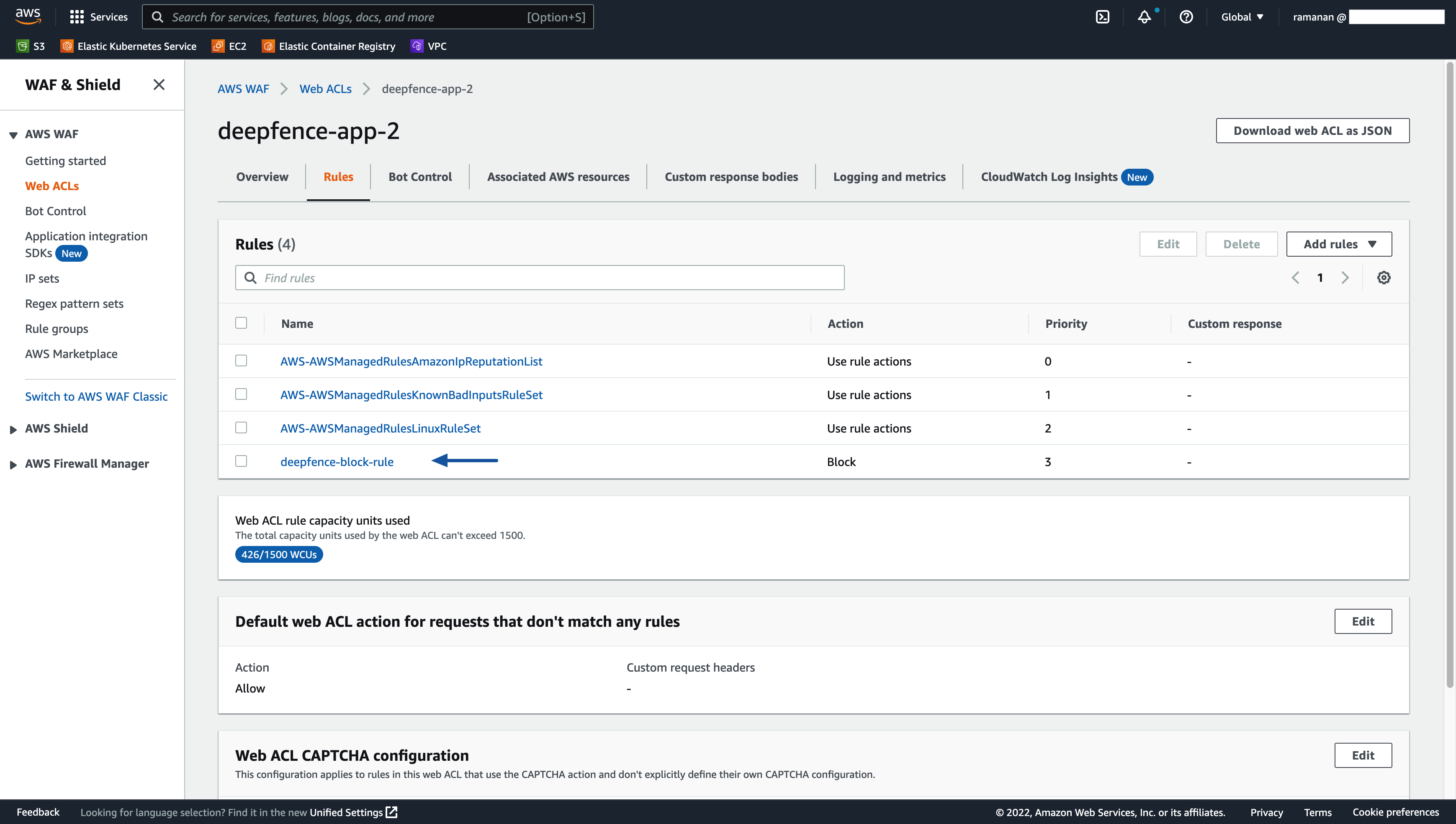
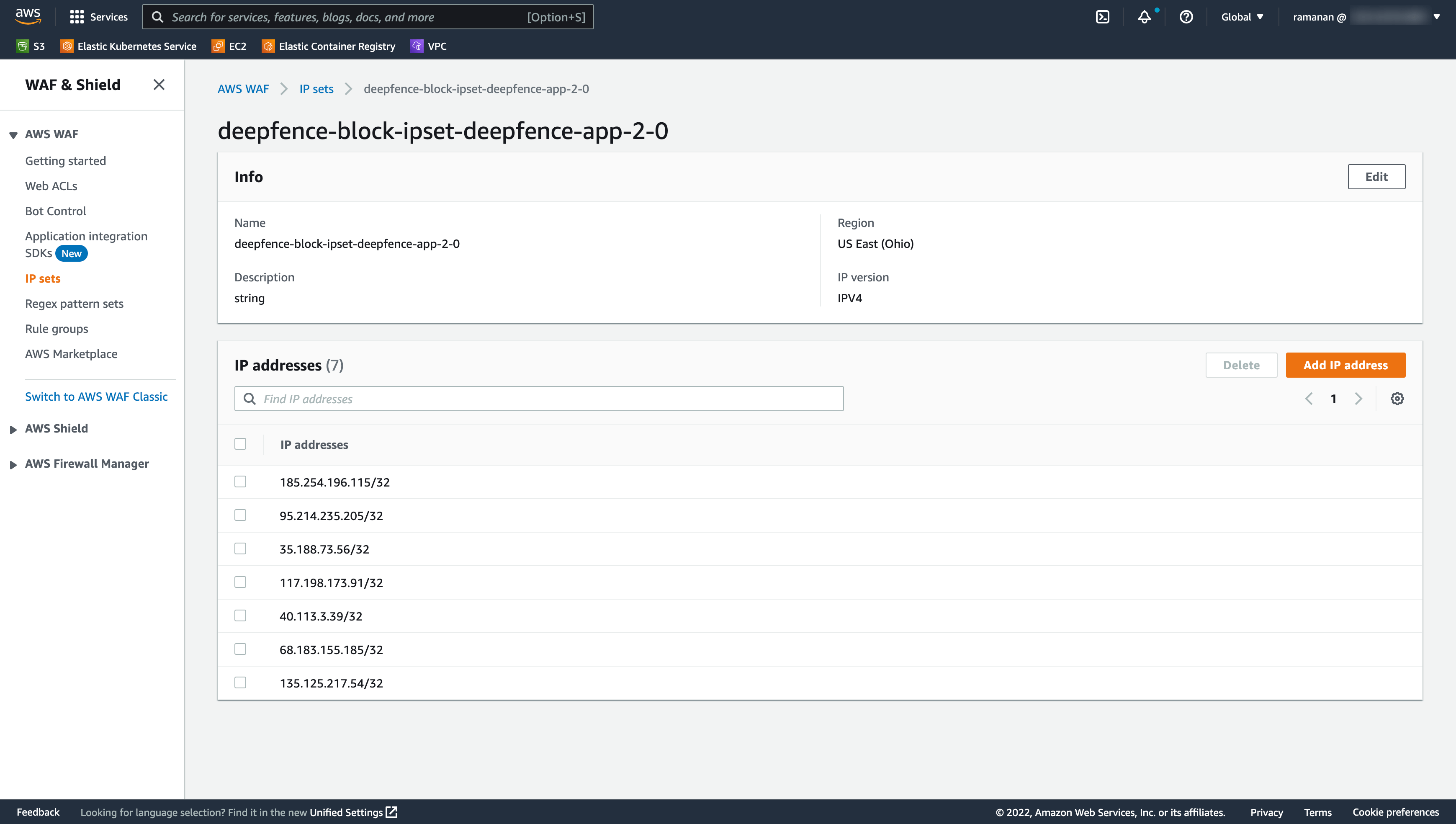
Network Protection Policy using Cloud WAF
Protection policy can be enforced using Cloud WAF if configured by the user. Only AWS WAF is supported at this moment. Deepfence will create IP Set and add a rule in the Web ACL's provided by the user.
IAM role
- Deepfence Management Console requires write permissions to WAF for policy enforcement.
- If console is deployed in a EC2 vm, add the policy
AWSWAFFullAccessto the instance IAM role.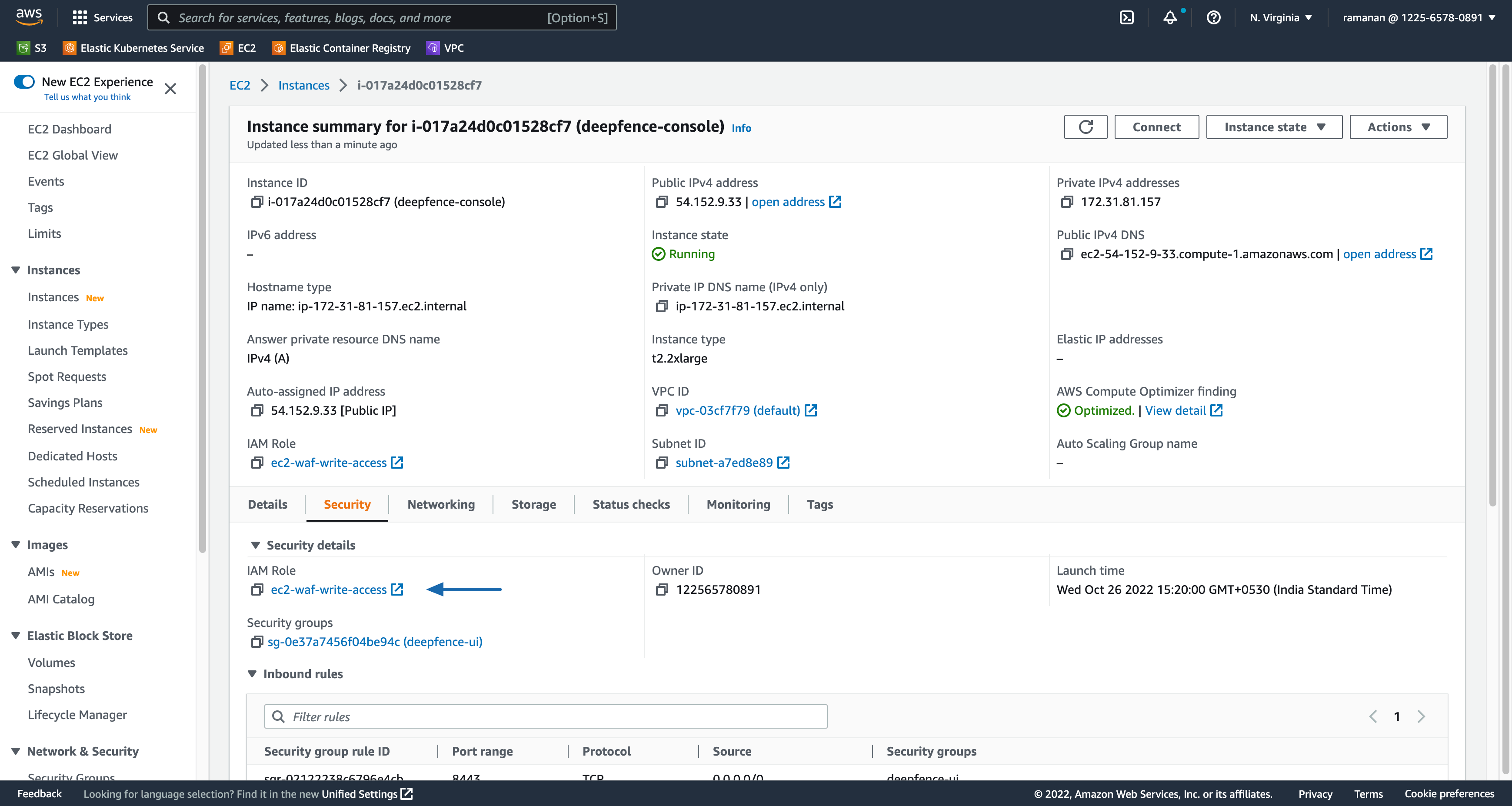
- In case of EKS (Kubernetes), this policy (
AWSWAFFullAccess) should be added toNode IAM roleof the node group.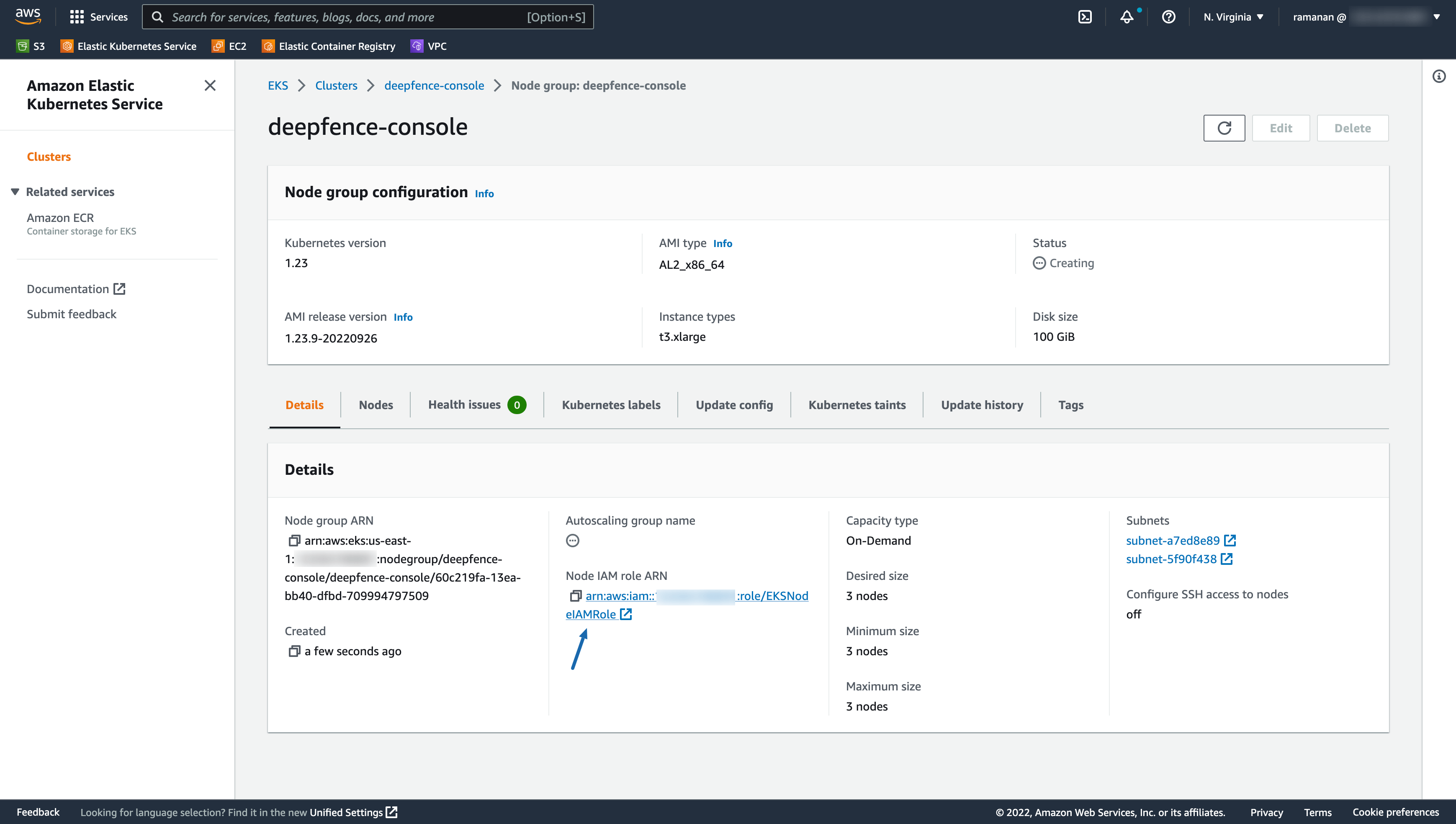
Configuration
- Copy ARN's of all Web ACL's in all regions that needs protection.
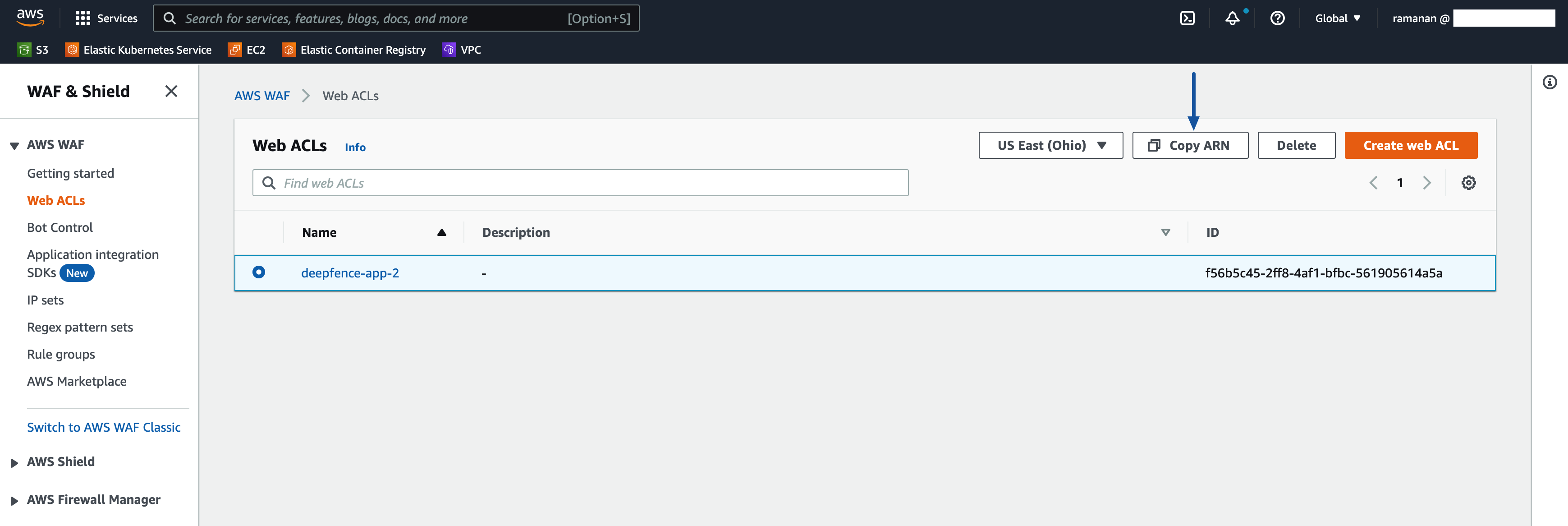
- Add the Web ACL ARN's in Deepfence settings and save.
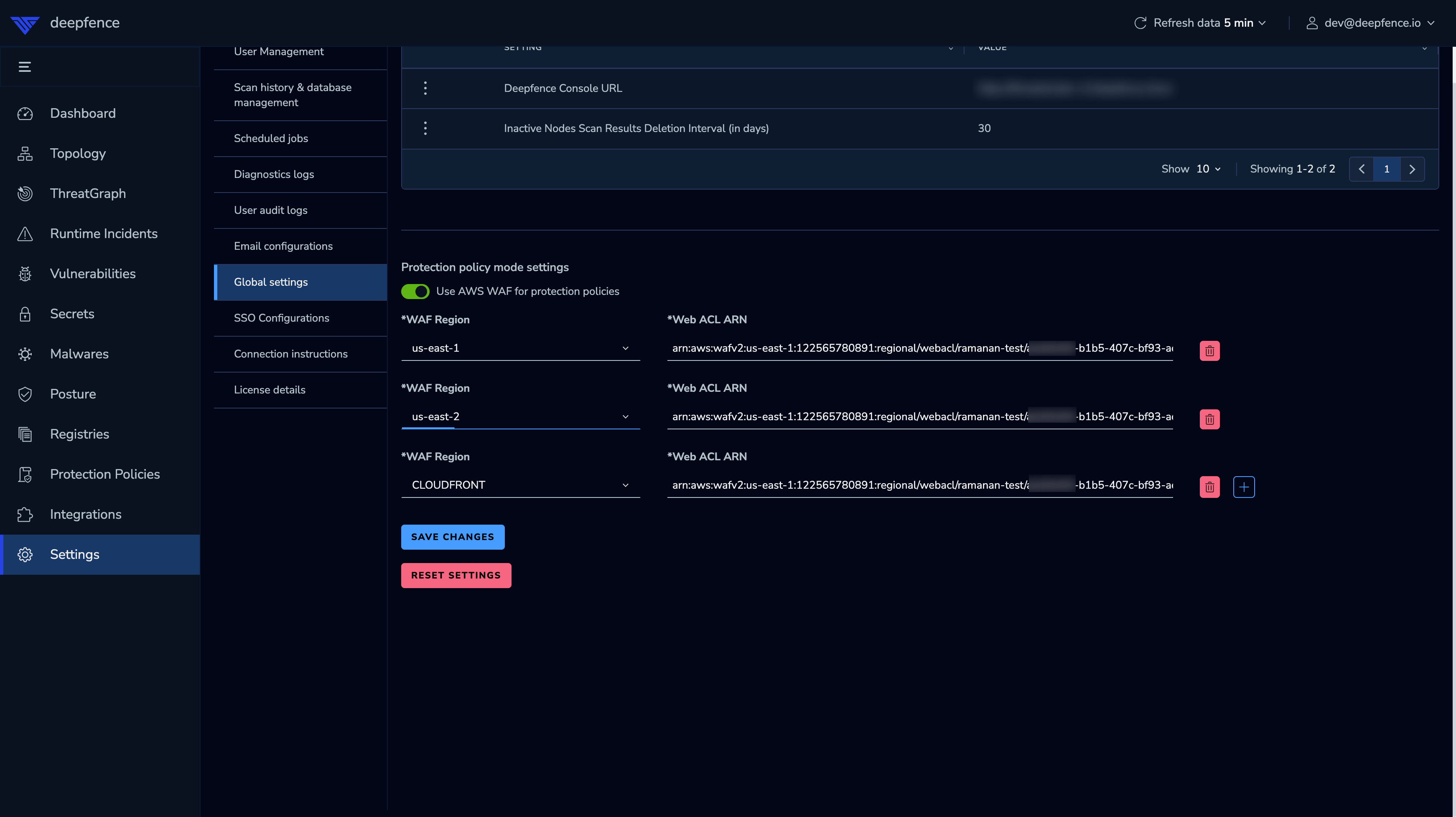
- Deepfence will automatically create IP Set for each Web ACL provided and update those Web ACL's with new rule.